
HackTheBox: Heist
The first step is to run Nmap to find what services are running on the host. # Nmap 7.70 scan initiated Wed Aug 14 21:08:24 2019 as: nmap -A -p- -oN scan 10.10.10.149 ...

The first step is to run Nmap to find what services are running on the host. # Nmap 7.70 scan initiated Wed Aug 14 21:08:24 2019 as: nmap -A -p- -oN scan 10.10.10.149 ...

This was such an easy machine, its almost not worth completing the write-up for it. But i decided in the end that i would, purely for completeness. I scanned the machine with NMAP, and was present...

The first step. As is almost always the case is to run an Nmap scan on the host to discover which services are running: root@kali:~/Documents/haystack# nmap -A -oN scan 10.10.10.115 Starting Nmap ...
this post describes the process of finding the user and root flags in HackTheBox Writeup machine. So as always start with an Nmap scan to discover which services are running. # Nmap 7.70 scan init...
The first step, as always, Is to Nmap the host to identify running services: Nmap scan report for 10.10.10.137 Host is up (0.042s latency). Not shown: 65464 closed ports, 66 filtered ports PORT ...

The first step is to Nmap the machine to find which services are running: root@kali://root/Documents/bastion# cat scan # Nmap 7.70 scan initiated Wed Aug 7 10:36:31 2019 as: nmap -A -oN scan -p-...

This is the second machine i have completed on HackTheBox. I started with the Access machine. So the first step to the perform an Nmap scan to see what kind of services the machine is running: nm...

I should preface this by saying that this machine took me about 6 hours to complete overall. I went down a couple of rabbit holes i didn’t need to go down and the final solution was much simpler th...
The following is a writeup on the process used to get the invite code for HackTheBox HackTheBox is a great website which contains pentesting labs to develop your security skillset. To create an ac...
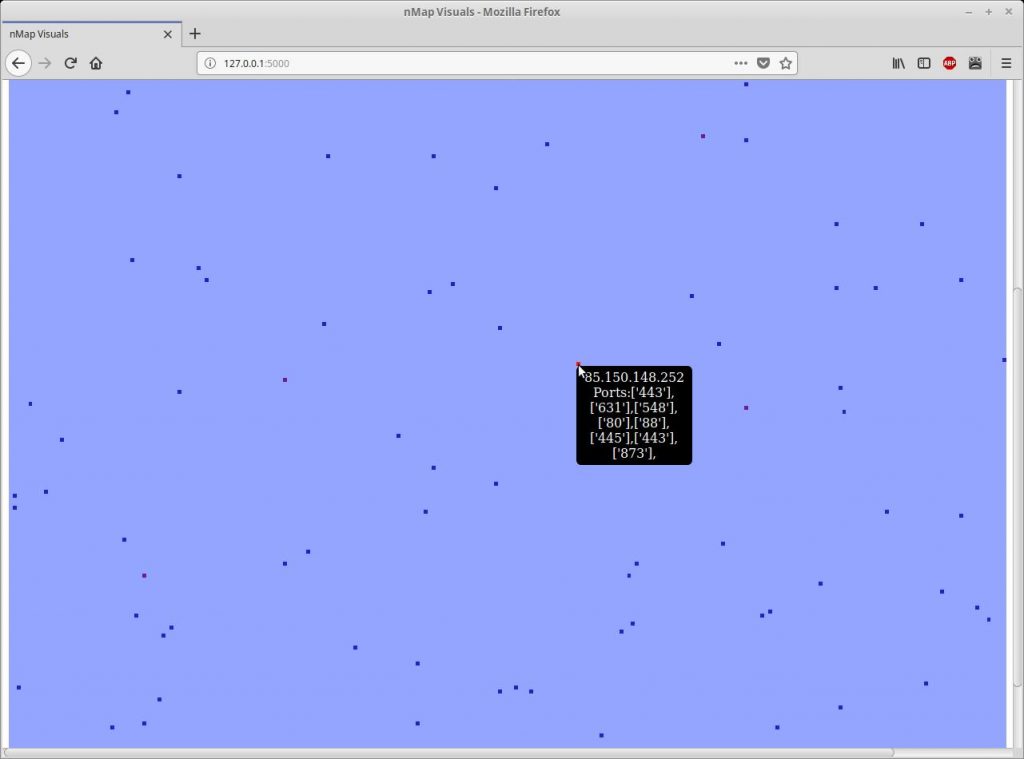
Introduction I have written a quick and dirty python script to visualise results from nMap and masscan. It works by parsing the XML log from a scan and generates a visual representation of the IP ...